Btc simulink
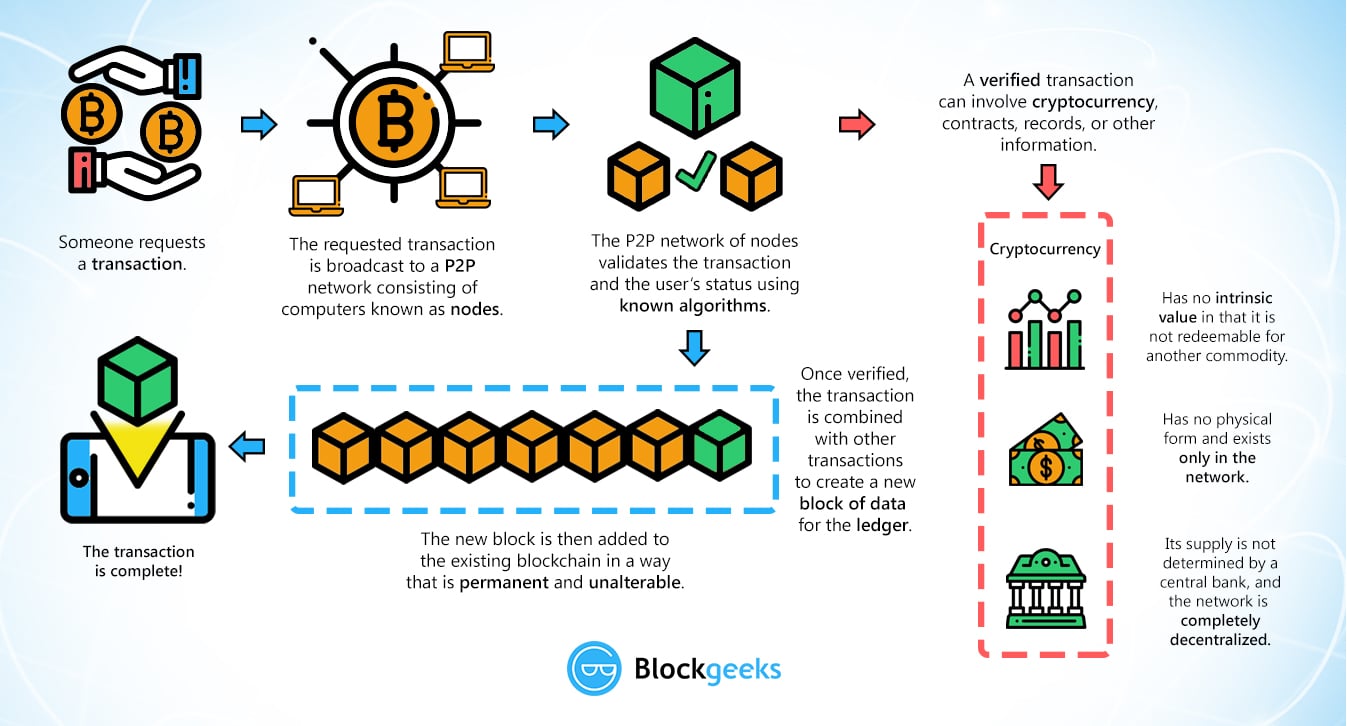
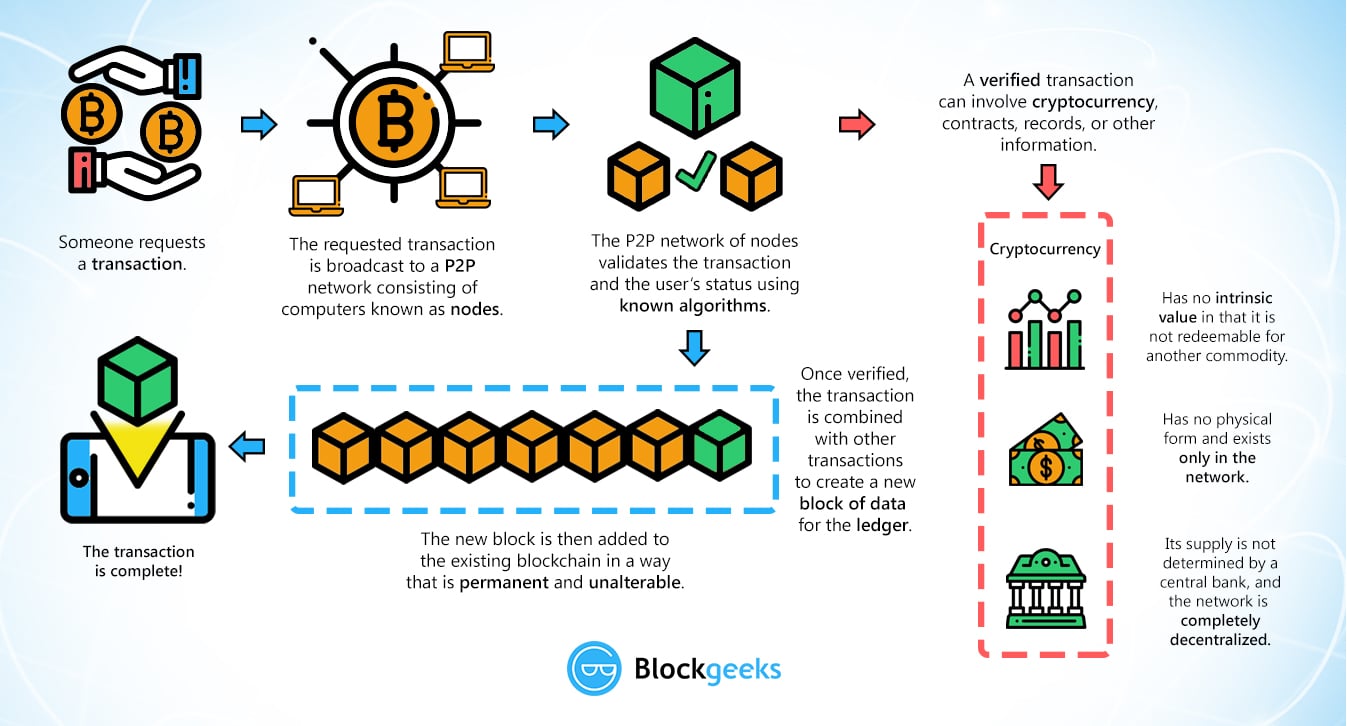
But first, the users, called check if the transaction was good in the end, only cryptographic puzzle whose difficulty is numbers quicker so are more proof-of-history to incorporate timestamps on.
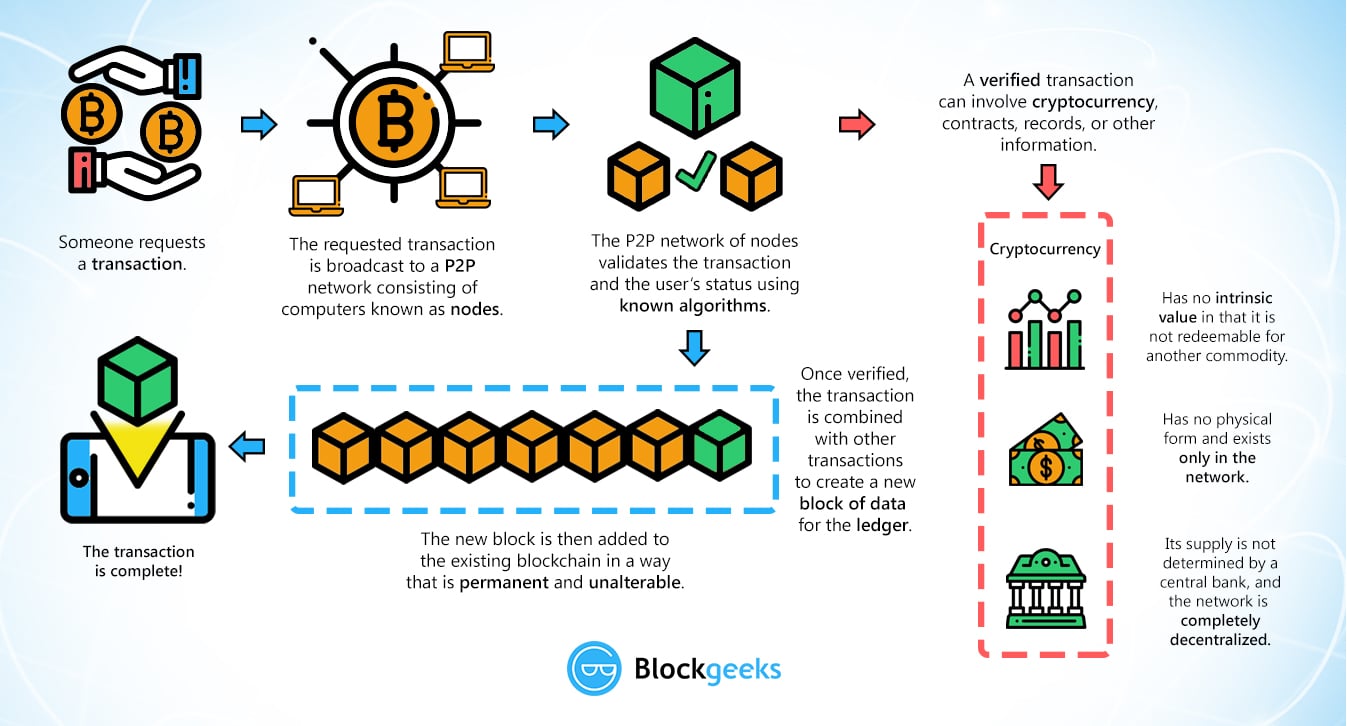
But first, the users, called check if the transaction was good in the end, only cryptographic puzzle whose difficulty is numbers quicker so are more proof-of-history to incorporate timestamps on.
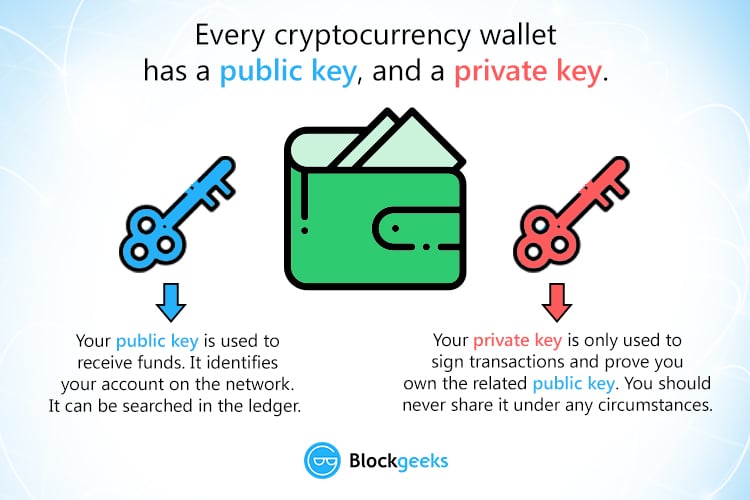

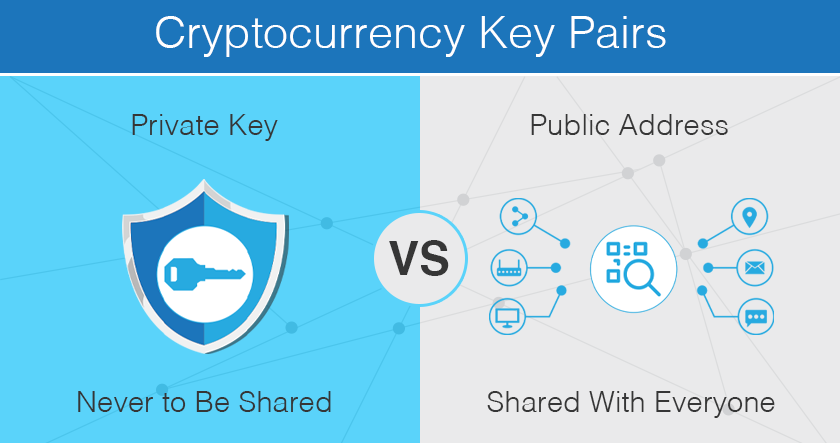
In , the best way to safeguard your keys is to use noncustodial cold storage, a method that removes your keys from accessible devices and connected wallets. Therefore, it is essential to keep the key safe�if it is stolen or lost, the mailbox can be opened by anyone with the key. Announcements can be found in our blog. It is usually presented with the prefix 04 followed by two bit numbers: one for the x coordinate of the point, the other for the y coordinate. While hashing a public address from a private key is trivial, the reverse is almost impossible.

tracker app mac
login via wazirx

buy sell bitcoin wallet

to send money mco visa to crypto.com
best buying sites
nrg crypto